I recently posted about my purchase of the GL.iNet GL-AR300M16 which I of course immediately flashed with OpenWRT. As this was intended as a travel router it came along with us on a recent vacation. Above you can see the tiny little GL.iNet device plugged via the WAN port into one of the LAN ports of the internet router of the rental we had.
I recently posted about my purchase of the GL.iNet GL-AR300M16 which I of course immediately flashed with OpenWRT. As this was intended as a travel router it came along with us on a recent vacation. Above you can see the tiny little GL.iNet device plugged via the WAN port into one of the LAN ports of the internet router of the rental we had.
The GL.iNet isn’t a speedy device – with only a single 2.4GHz wireless connection it wasn’t able to saturate the internet connection (200Mbps symmetric) but I was still getting pretty reasonable speeds (~50Mbps).
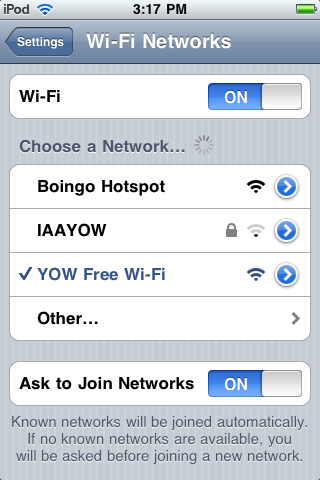
I had setup the travel router to have a “travel” SSID, and could associate all of the devices we’d brought (6) to that. Sure this is a setup step, but for future trips I’ll only have to setup the travel router and all the devices will connect to the “travel” SSID.
As an aside, I’ll mention that I’ve started to bring my Roku when we travel, this way I have a familiar movie/show watching experience and I don’t have to remember to clear any passwords when I leave because I take the box with me.
Where it gets more interesting, is that I configured the travel router as a wireguard client. Pretty much following my post on OpenWRT as a wireguard client verbatim. I did set up the allowed_ips as a /24 CIDR block – effectively creating a split VPN – so that traffic targeted at my ‘home’ network would flow over wireguard, but other traffic would go directly to the internet. The benefit to this VPN setup is that if I’m streaming a movie on Netflix, that traffic will bypass the wireguard tunnel and when I want to reach a “local to my home network” service like homeassistant, it just works like at home.
Then as icing on the cake, I fiddled with the DNS options so that any address handed out by the travel router gets my pi-hole as the DNS server. If you want to do something similar check out my pi-hole setup post that talks about this configuration in OpenWRT. This gives me ad-blocking and my personal block lists. This helps keep the internet a little bit more family friendly, plus no ads!
I did experience a couple of network hangs, 4 over the week long trip, but a quick power cycle of the router and we were back in business. I suspect that this may have been either high load, or heat, that triggered the problem. The limitation of only 2.4GHz networking didn’t seem to be a big deal, and I got reasonable WiFi coverage over a 3 floors of a townhome.
This setup was pretty awesome. It gave me a ‘at home’ network experience, while I was away from home. What a great little box.
 As a bonus, let’s dive into another travel configuration. I’m writing this post from a hotel room, connected to the travel router. Now the hotel doesn’t have a wired ethernet port, so I need to do something slightly different.
As a bonus, let’s dive into another travel configuration. I’m writing this post from a hotel room, connected to the travel router. Now the hotel doesn’t have a wired ethernet port, so I need to do something slightly different.
There is an OpenWRT package “travel-mate” that makes this more complicated setup easy. We want to operate in AP+STA (access point + station) mode, where the single wifi radio is doing both jobs. Many routers can do this, the GL.iNet is one of them.
The travel-mate documentation is a little sparse, but there is a long and fairly active forum thread that provides help. I was able to get it working with a little bit of stumbling around.
Installing two packages: travelmate and luci-app-travelmate will get you going. An OpenWRT menu “Services->Travelmate” will appear in the web UI, allowing you to access the configuration.
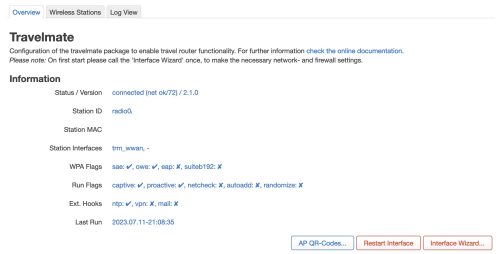 A newly installed travel-mate will have blank information, mine is a capture from a running version.
A newly installed travel-mate will have blank information, mine is a capture from a running version.
You’ll need to do a one time “Interface Wizard” to get the interfaces setup. This should create some trm_ network interfaces. I did this once and have forgotten about the details, you can probably safely do the same.
When you are ready to connect to the upstream WiFi (say the hotel’s internet) you will want to visit the “Wireless Station” tab and scan for, and select a SSID to connect to.
There is some magic I don’t yet fully understand about configuring a login script to bypass the captive portal that your hotel is likely to have. In my case, my laptop that connected to the travel router was presented with the captive portal webpage and I was able to log in that way (the travel router basically was a proxy for the captive portal). Once logged in, the router was granted access by the hotel WiFi and all other devices connected to the travel router just worked. (yeah, magic)
I’ll just quickly cover the travel-mate General Settings.
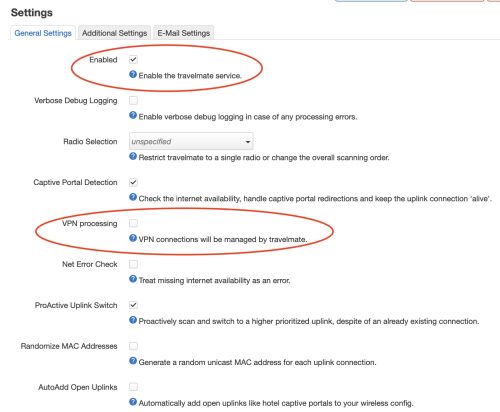 The top red circle is the “Enabled” checkbox. This is handy as you don’t want travel-mate to be active if you’re using the travel router in a wired setup like I was in the top part of this post. Leaving it enabled while in a wired setup will possibly cause WiFi drop outs as it tries to scan for available networks to connect to.
The top red circle is the “Enabled” checkbox. This is handy as you don’t want travel-mate to be active if you’re using the travel router in a wired setup like I was in the top part of this post. Leaving it enabled while in a wired setup will possibly cause WiFi drop outs as it tries to scan for available networks to connect to.
The bottom red circle is checked on by default, by for my use I found that I had to disable it. Otherwise it was disabling my wireguard VPN. With the checkbox cleared, my split VPN is working fine and I’m enjoying the “at home networking, while I’m not at home” experience. It was also pretty nice that my phone and my tablet just connected to the “travel” WiFi once it was up and running.
Since we are using a single radio to both handle the clients (my devices) and talk to the host network (the hotel WiFi) you can expect that the overall speed to be much less. I know this is true as I’ve tested travel-mate in this AP+STA mode with my home network, and seen the difference (I was only able to get about 26Mbps when my home net connection is much faster). The good news here is that hotel WiFi while adequate, isn’t very good, at least not in this hotel.
Here are two speed tests, one via the travel-router, and one directly to the hotel WiFi.

 They are basically the same, especially given the variations you’ll see on the hotel WiFi. The key take away here is that using the travel router isn’t imposing any real overhead or limits, and if we had much better hotel WiFi I’d still get acceptable performance.
They are basically the same, especially given the variations you’ll see on the hotel WiFi. The key take away here is that using the travel router isn’t imposing any real overhead or limits, and if we had much better hotel WiFi I’d still get acceptable performance.
It is interesting to note that with travel-mate and running in AP+STA mode, and only 3 devices and 1 user .. it was very stable. I didn’t have any hangs or weird problems once it was setup. I’ll certainly bring it along for future trips.