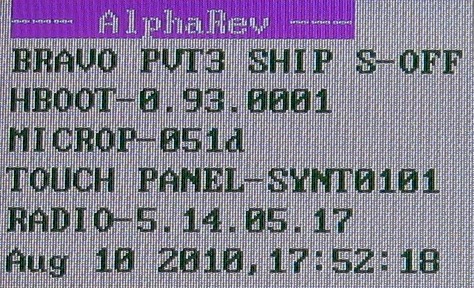
 HTC phones have a security flag, this flag is normally “ON” and is indicated on the bootloader screen as S-ON. The purpose of the security flag is to prevent unsigned firmwares from being installed. Clearly if you want to modify your phone with custom firmware you need to be in the S-OFF state.
HTC phones have a security flag, this flag is normally “ON” and is indicated on the bootloader screen as S-ON. The purpose of the security flag is to prevent unsigned firmwares from being installed. Clearly if you want to modify your phone with custom firmware you need to be in the S-OFF state.
To access the bootloader screen: start with the phone in a powered off state; hold the volume down button; then press the power button. This should result in you entering the bootloader screen. Menu navigation is via volume up/down and the power button for select.
My HTC Desire was in S-ON, yet still running custom firmware. This was done by Unrevoked3. It switched the phone to S-OFF, installed a custom recovery image, then switched back to S-ON. I believe since the recovery image has the ability to install firmware you can dodge the firmware signature check (effectively bypassing hboot). Really the only reason to have S-ON is to make the phone look more like stock.
There are multiple ways to achieve S-OFF (including Unrevoked3), but what I primarily wanted to do was change the partition table to allow for more application storage on the phone. The partition table is part of the hboot, so changing this is a bit scary since if you mess up hboot you have no easy path to recovery. The good (and bad) news is that S-OFF is also achieved by flashing a new hboot.
Custom partition table hboots are hosted on the AlphaRev site. It is a information dense site. If you plan to do this, read all of it carefully. If you really don’t understand what it’s talking about, read some more or consider asking someone for help. This is not something you want to get wrong.
As with anything like this – do a backup of your stuff. Download the iso from AlphaRev and burn a CD, you’ll be booting your PC into the custom linux based image to do the changes. The tool is well scripted and pretty clear. Do not panic, and read what is on the screen carefully. Once the AlphaRev tool is done, you’re phone will be in S-OFF state and should have a bootloader screen similar to what is at the top of this post
Now we’re in S-OFF mode, we can flash an hboot with a custom partition table. If you had already achieved S-OFF you could skip the above steps and just start here to customize your partition table. Here are the steps I took:
- Boot into your recovery image (ClockworkMod Recovery) and do a backup
- Verify the MD5SUM of the hboot file you downloaded
- Place the phone in fastboot mode (bootloader)
$ sudo ./fastboot flash hboot bravo_alphaspl.img(filename may differ) - Reboot the phone
$ sudo ./fastboot reboot-bootloader - Erase the cache
$ sudo ./fastboot erase cache - Boot into your recovery recover image
- Wipe everything using recovery
- Restore the backup you made
If your phone is stuck in S-ON, then fastboot isn’t an option.
The benefits of the custom partitions is significant. The NexusOne had 196MB of internal storage, the stock HTC Desire only 148MB. With the custom partition table hboot, I now have 288MB. The trade-off is the partition table I’m using now won’t fit the stock ROM, but reverting to a different hboot is easy enough by repeating the steps above.
You’ll notice that the AlphaRev process customizes your splash screen. If you’re not happy with this they provide a link to the stock splash screen. Enter the bootloader again, and issue:
$ sudo ./fastboot flash splash1 desire_stock_splash1.img
And you’ll be back to looking like stock. Creating your own custom splash screen is also quite easy to do. If I get inspired to change mine, I’ll write up details on how – but a bit of searching will get you the answer too.







